
PCI DSS AWARENESS TRAINING
Book a free demo
This entry-level course outlines the challenges surrounding payment card security and explains what the PCI Standards do to mitigate these issues – and will provide you with the tools to build a secure payments environment. Areas covered by the course include.
-
About this course
Payment Card Industry (PCI) Awareness training is for anyone interested in learning more about PCI – especially people working for organizations that must comply with PCI Data Security Standard (PCI DSS). By promoting employee awareness of security, organizations can improve their security posture and reduce risk to cardholder data.
-
What will you learn by taking this course?
You will learn how to secure your customer data and also below point
✅ Have tools and insight to build a secure payments environment
✅ Support your organization’s compliance efforts through your knowledge of how to apply PCI Standard
-
Why should you take this course?
This course Design for financial institute,Bank Technical Support Engineer & Technical Engineer and Manager. PCI DSS stands for Payment Card Industry Data Security Standard, which sets the requirements for organizations and sellers to safely and securely accept, store, process, and transmit cardholder data during credit card transaction to prevent fraud and data breaches.
-
Chapter 1: Introduction
✔️ PCI Data Security Standard (PCI DSS)
✔️ What is the role of the PCI Security Standards Council?
✔️ Are there any benefits to PCI DSS compliance?
✔️ What is the Payment Card Industry Data Security Standard
✔️ Where can I find the list of PCI DSS requirements?
-
Chapter 2: Importance of PCI DSS compliance
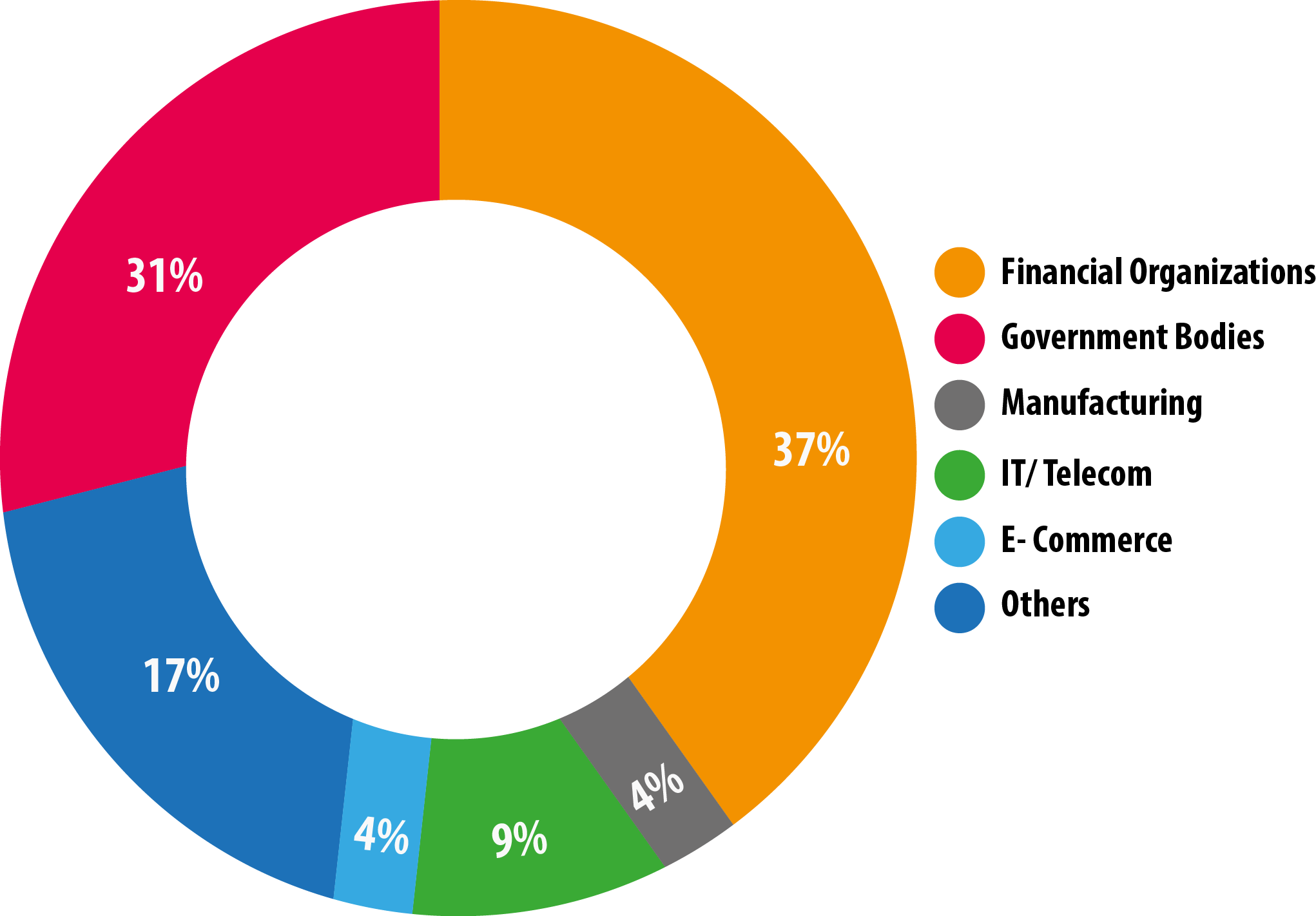
✔️ What kinds of organizations may be impacted?
✔️ Why is PCI DSS compliance important?
✔️ What happens to a small business when they don't know?
✔️ Who enforces the PCI DSS requirements?
✔️ Do the PCI DSS requirements apply?
-
Chapter 3: Validation Requirements of PCI DSS compliance
✔️ How often is PCI DSS validation required
✔️ What kind of vulnerability scanning is required
✔️ What is PCI PFI.
✔️ What are the PCI DSS compliance validation requirements
✔️ If organization is certified as PCI compliant, does it mean secure.
-
What does PCI DSS compliance mean?
PCI DSS stands for Payment Card Industry Data Security Standard which sets the requirements for organizations and sellers to safely and securely accept, store, process and transmit cardholder data during credit card transaction to prevent fraud and data breaches.
-
Who needs PCI DSS compliance certification?
Although there is technically no such thing as “PCI certification” sellers of all sizes, service providers, banks and any other organizations that process credit card payments need to prove they are PCI compliant.
-
What are the PCI DSS compliance levels?
There are four levels of PCI compliance; each level has unique requirements for a business to validate its compliance. The level under which your business falls is based on your total transaction volume, annually.
-
What does it cost to be PCI DSS compliant?
The fees to become PCI compliant, and maintain that standing annually, can range from approximately $1,000 annually to over $50,000 annually, depending on the size of your business.
-
Am I responsible for a PCI DSS Compliance Self-Assessment Questionnaire (SAQ)?
The PCI DSS Self-Assessment Questionnaire is a checklist ranging from 19 to 87 pages, created and distributed by the PCI Security Standards Council. It’s used as a mechanism for sellers to self-validate their PCI DSS compliance. Square does not require sellers to complete an SAQ, or to self validate, since Square’s hardware and software complies with the Payment Card Industry Data Security Standard (PCI DSS).
-
Is there a PCI noncompliance fee?
Yes, there are typically fees associated with PCI noncompliance. If your business does not comply with PCI standards, you could be at risk for data breaches, fines, card replacement costs, costly forensic audits and investigations into your business, brand damage and more.
- Key Features:
- Created by a Security expert :
- Access period : 12 months
- Course duration : 40+ hours
- Quizzes & revision exams :
- Certificate of completion :
- Support : 24/7 hours
What is PCI?

The PCI is a financial industry sector that is in charge of all electronic payments. Sensitive financial data is continually communicated to all areas of the world when purchases are made through debit, credit, ATM, POS, prepaid, and e-purse systems.
What is PCI DSS?
Merchants and vendors must follow the Payment Card Industry Data Security Standard (PCI DSS) to secure cardholder data. The PCI DSS defines a minimum degree of security for enterprises that store, handle, or transmit payment card data.
Who Must Comply with PCI DSS?

The term "standard" in the PCI Data Security Standard may lead some to assume that PCI compliance is a "nice to have" rather than a "must have or else." In actuality, the PCI DSS is a regulation. Consider this: the credit card companies who offer credit/debit cards to ordinary people (your customers) will permit you to process those payment cards. The credit card companies will not allow you handle their payment cards if you do not comply with the PCI DSS compliance rules. Furthermore, you may face a monetary penalty. The PCI Data Security Standard is not optional unless you want to operate a "cash only" firm
CRITICAL TRAINING FOR HANDLING CRITICAL DATA
The engaging, interactive PCI DSS and PCI compliance training courses offered by Aspire enable cardholder data handlers and supervisors to achieve PCI compliance, pass audits, and avoid data breaches.
PCI DSS Awareness Module
Your personnel will be able to properly manage credit card data with the PCI DSS awareness module. Understand the PCI DSS regulations, how to maintain data and accounts securely, and how to spot and respond to security breaches.
Common Cases Of Data leaks
A data breach is terrible news for any company. If the leaked information is connected to credit card information, your company will have a major data security and compliance problem to deal with. A data breach might happen in a number of ways. Take a look at a few examples:
Human Error
Data breaches are frequently caused by human mistake. Many businesses place a premium on technological issues that lead to breaches and fall behind in attempts to address human factors through Security Awareness Training.
Insider Threat
One of the other major causes of a data leak is an employee or contractor having authorized and privileged access to internal organizational resources
Malware
Many individuals believe that malware produces damage in a single, quick burst and then vanishes. In truth, some of the most dangerous viruses may hide in plain sight and steal data for years before being identified.
Unpatched Software
Data breaches are frequently caused by software and systems that have been left unpatched for an extended period of time. Infrastructures grow infested with known vulnerabilities over time, eventually becoming the source of a data leak.
How to Detect Data Leaks
Data Breach Assessments
Many sophisticated assaults are designed to remain undetected for as long as feasible. As a result, data leak/breach evaluations should be performed at least once every quarter for large businesses and once every six months for smaller ones.
Monitor
Data breaches can, of course, be detected through internal audits and testing. Also, keep an eye on the dark web for signs of your company's data. It's a huge red flag if you can find your company's details there.
Data Leak Prevention (DLP)
DLP software functions as a firewall between outsiders and sensitive data within the company. Insider dangers can also be detected. It employs a number of criteria to detect sensitive information and actions that may result in unintentional exposure. In today's cybersecurity threat landscape, investing in a solid DLP should be viewed as a "must-have."
Comprehensive Analysis
Conduct a comprehensive examination of all important systems and devices' processes and services. Conduct a thorough network traffic analysis as well. If done in-house, the inquiry may become a black hole that eats up time and money. To save time and money, consider hiring an expert to do the exam.
How to Prevent Data Leaks
Human Firewalls
Teach your employees how to spot and avoid hacker traps. If just one employee clicks on a phishing email or accesses a harmful website, all the technical defenses in the world won't help.
Technology
Invest in a reliable Data Leak Prevention system. When setting up your DLP, make sure you know what data is critical to your company and that you have procedures in place to protect it.
Encryption
Encryption is essential for the security of payment card data in general. On all PCs, gadgets, and mobile devices, make sure you employ strong encryption.
Regulations
Organizations maintain basic security and reduce the risk of regulatory fines by adhering to data protection standards. Develop a data security and compliance plan, as well as policies and processes to support data privacy and security, to stay compliant.
Monitor & Track
Don't allow a false feeling of security to sneak into your company just because you've invested in advanced cybersecurity software and tools. Manual monitoring, tracking, and human instinct remain critical components of cyber defense. Similarly, never believe that outsourcing information security functions ensure that your data is secure.
Boost Engagement with delivering Communication Tools

Increase employee engagement with a different suite of communication tools like:
Posters
Promote your training program with visuals you can customize to brand... more
Newsletters
Send training updates and security best practice highlights directly... more
Digital wallpapers and web banners
Increase program engagement with colorful thought-provoking messaging... more
Training Videos/Animations
Strengthen key awareness concepts and skills through stylish visual... more
Why Aspire Tech
Award-winning courses
Aspire's award-winning online courses and programs are created and delivered by a renowned Cyber Security specialist.
The perfect fit for business
Plans for small to large businesses that are flexible to match your budget. There is a volume discount available.
Cost effective training
For a fraction of the expense of traditional classroom training, train thousands of employees in numerous locations.